WordPress Backdoors: 5 Easy Steps to Find and Clean Them
by
7-layers of Security for Your WordPress Site
Your website needs the most comprehensive security to protect it from the constant attacks it faces everyday.
Does your WordPress site keep getting hacked, even though you’ve cleaned it up many times?
You’ve spent ages fixing everything, only to see the problems pop back up. Your hacked site may be running slow, showing strange pop-ups, or experiencing unwanted changes. But you just can’t seem to find the cause.
These could be signs of a WordPress backdoor on your site.
It’s like a hidden key that lets hackers slip in and cause chaos. They can steal sensitive data or alter your site without your knowledge.
Backdoors cause trouble for many WordPress sites, not just yours. 30% of all websites fall victim to hacks because of backdoors and other vulnerabilities. The thought of someone sneaking into your site is creepy, especially if you’re not a tech expert.
But don’t worry. In this article, we’ll explain how you can find them and close them for good.
TL;DR: WordPress backdoors are sneaky entry points that hackers use to get into your site. They can make your site slow and even change things without your OK. Finding and removing these backdoors is essential for keeping your site secure. To make this easier, use a security plugin. It can help detect, remove, and block backdoors efficiently.
What is a WordPress backdoor?
WordPress backdoors can come in many forms. They might be tiny bits of harmful code or simply full files. They can also take the shape of hacked admin accounts, malicious cron jobs, or loose file permissions set by hackers. These are ways hackers keep an open door to your site. Anything that lets them control your website remotely can be a backdoor.

The hard part? They often look like regular files, so they’re tough to spot. Even if you delete the main malware, a backdoor might still be there, ready to cause more problems. It’s like searching for a needle in a haystack, except the needle looks just like the hay. That’s why backdoors are tricky—they’re sneaky and stubborn.
💡 The only way to find backdoors effectively is to scan your site for malware.
Step 1: Check signs of a WordPress backdoor on your site
Think there might be a backdoor in your WordPress site? If you see odd changes, unexpected pop-ups, or slowdowns, your site might be hacked through one. Here’s how to find out if there’s a backdoor:
1. Run a security scan: Use a security plugin to scan your site. Not all scanners catch backdoors, but some, like MalCare, do. It looks for harmful code and suspicious files, giving you a clear view of hidden threats.
2. Watch out for unusual site behavior: Is your site suddenly slow or crashing a lot? These issues could mean a backdoor is letting a hacker mess with your site from within.
3. Check for unwanted content: Look for strange ads, spammy links, or new pages you didn’t add. Hackers might use a backdoor to insert this unwanted content and mislead visitors.
4. Look for odd user accounts: Regularly check user accounts. If you see new ones you didn’t create, hackers might have added these to keep control of your site.
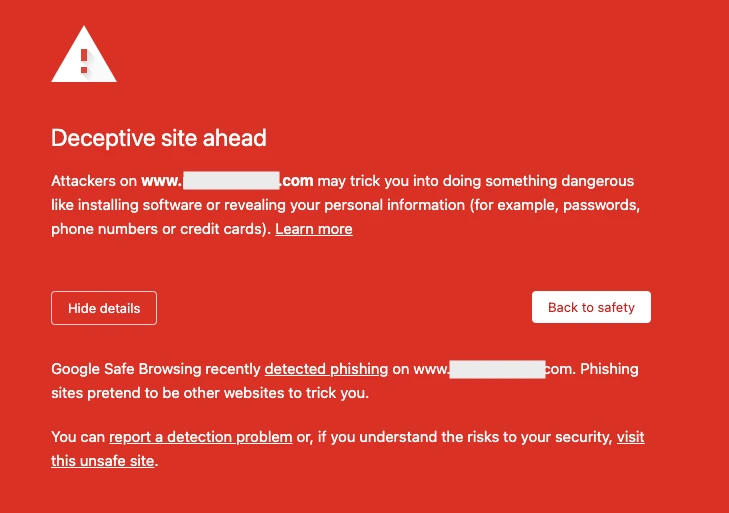
5. Notice search warning signs: If search results show warnings like “This site may harm your computer” or “Deceptive site ahead,” that’s a big red flag. It usually means there’s harmful activity tied to backdoors or other malware.
6. Check for changed files: File changes you didn’t make can signal a hacker accessing a backdoor. Look through your file directories for anything unusual.
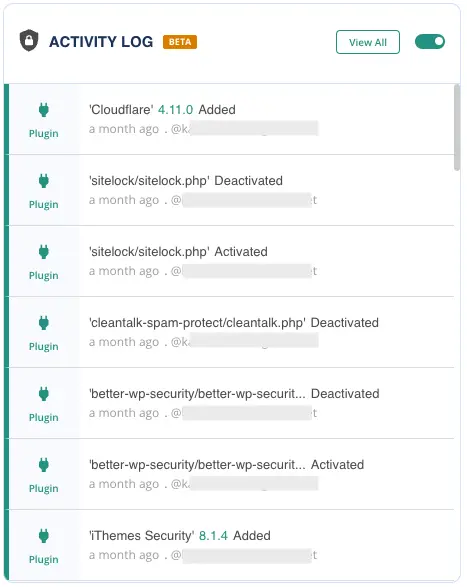
7. Examine site logs: Your site logs provide clues to suspicious actions, like repeated login attempts or unauthorized admin access. Strange patterns can point to a backdoor. MalCare’s activity logs can help you watch these closely.
8. Watch traffic patterns: Unexpected traffic from unknown IPs or sudden visits from new countries might suggest a backdoor is in use. Check your site’s traffic analytics for these signs.
If you spot any of these signs, a backdoor might be on your site. Now, let’s focus on removing it. Follow these steps to secure your site and kick out hackers for good.
Step 2: Scan your site for a WordPress backdoor
Start by scanning your site with a security plugin, like MalCare. It digs deep into your site’s files and database to find any stubborn malware. It spots hidden threats in scripts, plugins, and database entries. With a thorough scan, you’ll clearly see potential vulnerabilities and malicious code. This step is key to making sure your cleanup is complete.
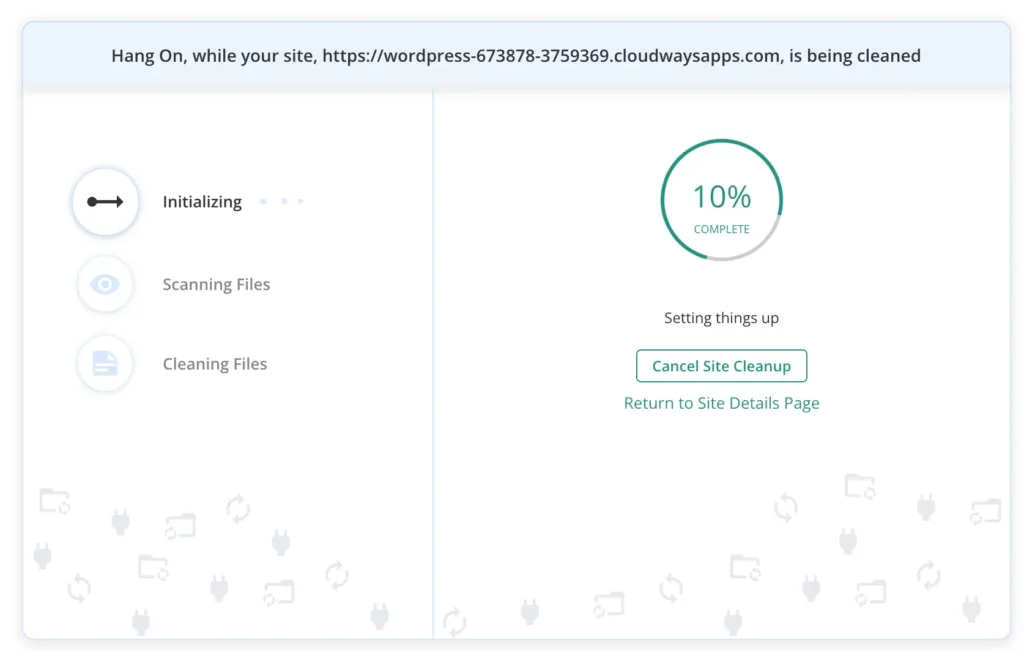
Step 3: Clean the WordPress backdoor, if found
After the scan, clean up the malware found. MalCare does more than just detect threats—it removes them too, ensuring nothing sneaky remains. If any files were affected, restore them from a clean backup. By thoroughly removing all malware, you’ll bring your website back to its secure state. This sets the stage for taking steps to prevent future breaches.
Step 4: Checklist for post-WordPress backdoor removal
After removing the malware, it’s important to verify that your site remains secure and nothing was missed. Follow this checklist to protect your website and ward off future attacks.
1. Change all your passwords: This step stops hackers from using old credentials.
a. Reset admin passwords: Create strong, unique passwords. A password manager can help with this.
b. Inform your users: Ask everyone with site access to reset their passwords. Stress on the importance for strong and unique passwords.
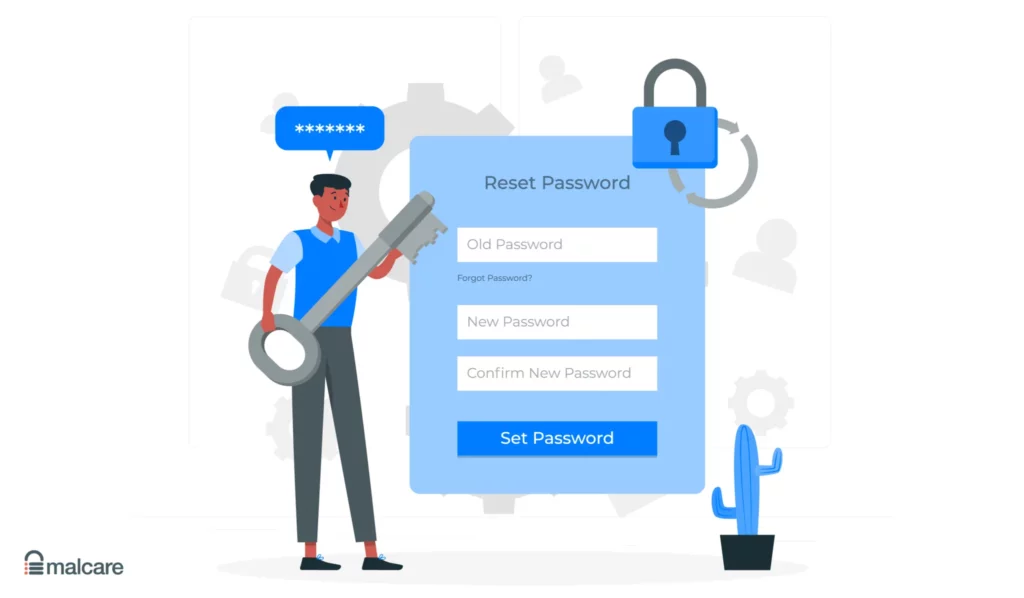
2. Update all your software: Hackers love outdated software. Check for updates for your CMS, plugins, themes, and other site-related software. Apply any updates right away to patch vulnerabilities and boost security.
3. Boost your site’s security measures:
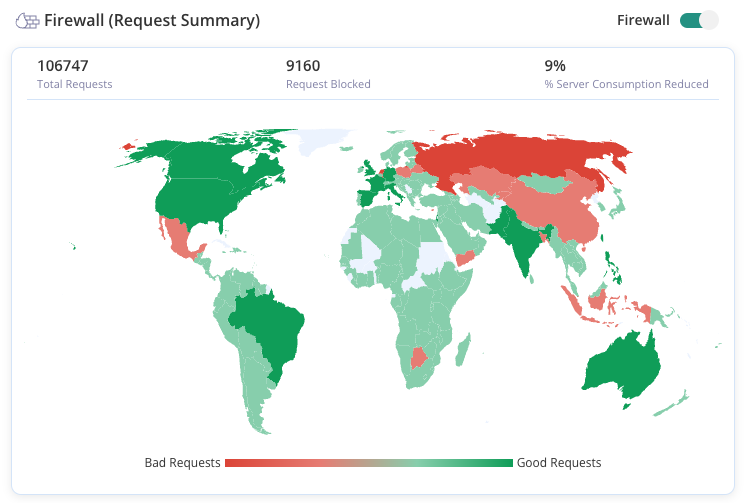
a. Install a web application firewall (WAF): A WAF blocks malicious traffic and attempts to exploit your site. MalCare offers the Atomic Security firewall, always working to keep your site safe.
b. Limit login attempts: Restrict the number of failed logins to prevent brute force attacks.
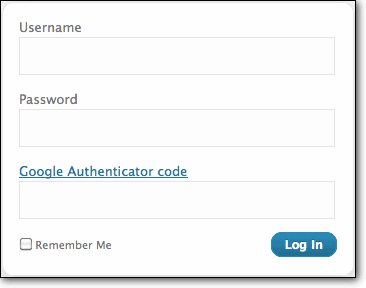
c. Install two-factor authentication (2FA): Enabling 2FA adds an extra security step to your login. This makes it tougher for unauthorized users to break in.
Step 5: Prevent a WordPress backdoor in the future
You’ve cleared out the WordPress backdoors, but how do you make sure they don’t come back? It’s about taking proactive steps. Here’s how you can future-proof your website against backdoors:
1. Use a security plugin: Install a security plugin that scans for vulnerabilities and malware, removing them in real time. It’s like having a tireless guard watching over your site.
2. Use a web application firewall (WAF): A WAF filters out malicious traffic, acting like a moat around a castle. Invest in a trusted WAF to block attacks and prevent unauthorized access. MalCare’s Atomic Security firewall learns from vulnerabilities to secure your site even against zero-day threats.
3. Keep everything up-to-date: Hackers love outdated software. Update your WordPress core, plugins, themes, and related software regularly. Updates fix known vulnerabilities and keep your site secure. This is just like regular car maintenance that keeps your vehicle running safely.
4. Use complex passwords and change them often: Strong, random passwords are essential. Use a password manager to create and store them. Encourage your users to do the same to strengthen your security.
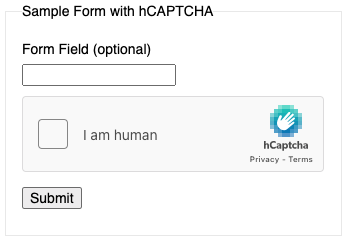
5. Put in place login security measures: Extra login security helps a lot. Two-factor authentication (2FA) and CAPTCHA work like extra locks, making it tougher for intruders.
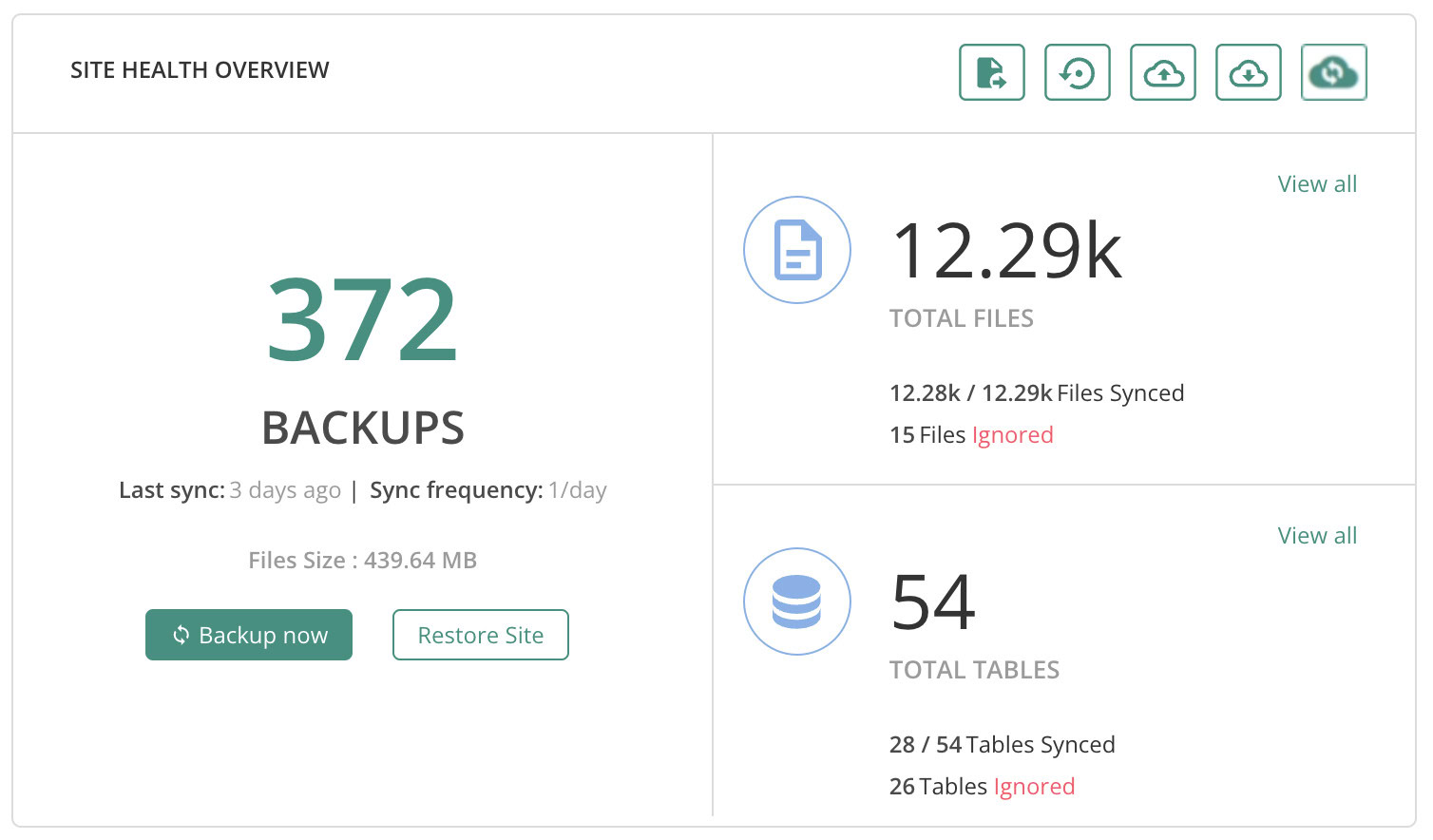
6. Take regular backups of your site: Back up your site often so you can restore it quickly if needed. Store backups in a secure, off-site place. MalCare’s backup feature ensures you’re covered here.
7. Regularly check site logs: Keep an eye on site logs to catch suspicious activities early. Look for unusual logins, file changes, or other oddities. Monitoring is like checking your bank statements for anything unusual. MalCare’s activity log feature helps track site happenings.
8. Regularly audit site users and their roles: Check user accounts and roles frequently. Remove inactive or unknown accounts and ensure permissions are necessary and minimal.
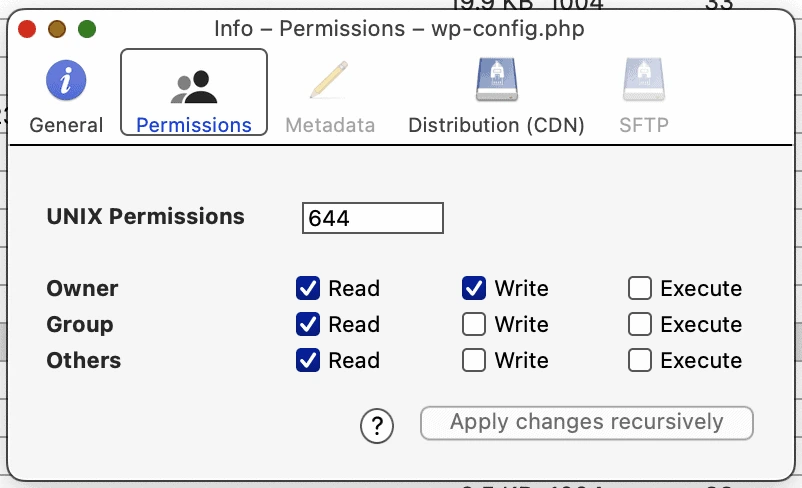
9. Set proper file permissions: Make sure your site’s file permissions are correct to limit user actions. Use the least privilege principle, giving only necessary access.
10. Educate site users and visitors: Teach users and visitors about threats like phishing and social engineering. Informed users are less likely to fall victim, adding extra security to your site.
How do WordPress backdoors get installed?
You might wonder, “How do these sneaky backdoors get into my website in the first place?” Hackers have a few common tricks. Let’s explore how these unwanted visitors often break in:
1. Vulnerable plugins and themes: Plugins and themes enhance your site’s functionality and design. But, they can also invite backdoors. Poorly coded ones often have security gaps that hackers exploit to slip in malicious code.
2. Outdated software: Running outdated software is like leaving your door unlocked. Hackers target sites using old versions of WordPress, PHP, or other software. These versions often have known vulnerabilities that make easy targets.
3. Weak passwords: Simple passwords are a hacker’s best friend. They can easily crack them to access your admin area. So avoid passwords like “password123” or “9876543210.” Also, change default passwords; many sites still use “root” for phpMyAdmin.
4. Social engineering: Hackers sometimes use tricks, not just technical skills. Phishing emails can fool you or your team into giving away sensitive info. A seemingly harmless email might get you to click a bad link or share login details.

5. File upload vulnerabilities: You should secure functions such as file uploads, like profile pictures or documents, if your site allows for it. Otherwise, hackers could upload malicious scripts disguised as safe files.
6. Server vulnerabilities: The security of your web hosting environment is key. Misconfigured servers or hosts that neglect security make your site vulnerable.
Why are WordPress backdoors dangerous?
WordPress backdoors are more than hassles. They’re serious threats to your site’s security, integrity, and reputation. Here’s why they’re so dangerous:
1. They can spread malware: Once hackers get in through a backdoor, they can use your site to spread malware to visitors’ devices. Like a virus spreading, what starts on your site can affect many others, causing wider harm.
2. They steal sensitive information: Backdoors open the door to data theft. Hackers can grab user info, payment details, and sensitive business data. It’s much like a thief sneaking off with your valuable documents.
3. They can deface your website: With control of your site, attackers can change content, show offensive messages, or crash it. This damages your site’s look and hurts your brand’s image, like graffiti on a storefront.
4. They overload server resources: Backdoors can launch unauthorized scripts that hog server resources. This can slow down your site. This can lead to frequent crashes, like a power surge from too many appliances on one outlet.
5. They make users distrust your site: Users who see malware, phishing, or defaced pages will quickly lose trust. Lost trust is hard to regain and can hurt your traffic and business. It’s like avoiding a restaurant with a health violation.
6. They drain your time and resources: Handling backdoors is time-consuming. You end up in a cycle of getting hacked and cleaning up, distracting you from focusing on your site and visitors.
Final thoughts
Keeping your website safe from backdoors is crucial for a smooth online experience. WordPress backdoors let hackers sneak in and mess with your site without you knowing. Learn to spot signs of a hack, use tools to find issues, and clean them up to keep your site protected. Regular updates, strong passwords, and good security habits are super important in stopping future problems.
For extra protection, use MalCare. It scans for malware in real-time and removes it automatically. MalCare also has a strong firewall and does regular backups to keep your site safe. You can find and remove backdoor malware easily with MalCare, without needing to be a tech expert. If your site does get hacked, MalCare helps you fix it quickly. With MalCare, you’ll know your website is protected, so you can focus on growing your online presence.
FAQs
What is a WordPress backdoor?
A backdoor in WordPress is a malicious program or code that is inserted into a website to bypass normal authentication or security measures and allow unauthorised access or control.
Can backdoors be detected?
Backdoors can be difficult to detect because they are designed to remain hidden and avoid detection. However, website owners can use security tools to scan their website for vulnerabilities and malware and monitor their website for suspicious activity to detect any backdoors that may have been installed.
What is a WordPress backdoor hack example?
A backdoor example is the CryptoPHP backdoor, which was discovered in 2014 and was embedded in pirated versions of popular WordPress themes and plugins. The backdoor allowed attackers to gain control of the infected websites and use them to launch further attacks.
What is the purpose of a backdoor?
The purpose of a backdoor is to provide unauthorised access or control to a computer system or network. Attackers can use backdoors to steal sensitive data, inject malware or spam links, or use the infected system to launch further attacks on other systems. Backdoors can also be used to maintain access to a compromised system, even if the original vulnerability that was used to gain access is patched.
Where is the backdoor in my WordPress site?
A backdoor can be anywhere on a WordPress site: the core files and folders, plugin files and folders, theme files and folders, and even in the database. Typically, they are hidden from view, and made to look like legitimate files.
How to scan for WordPress backdoor code?
The best way to scan for WordPress backdoor code is to install MalCare on your site, and set it up for scanning. MalCare will alert you of any malware that is found on your site.
How to tell if WordPress plugin has a backdoor?
Generally speaking, good plugins from reputable publishers will not have backdoors. This is usually a problem with nulled premium plugins from scammy sites. If you suspect a plugin you have installed has a backdoor, use MalCare to scan it for malware.
How to find a backdoor in a hacked WordPress site and fix it?
You can find a backdoor in a WordPress site by using MalCare. MalCare scans every file and folder on your site, and the database for good measure. It can ferret out the smallest, most well-hidden bit of malware.
Category:
Share it:
You may also like
WordPress Nonce – All You Need To Know About It
Ever clicked a link on a site and gotten a confusing error message instead of the page you expected? Maybe you were trying to submit a form or delete a…
2 Simple Fixes For index.php File Corrupted on WordPress Site?
Dealing with broken links and jumbled pages is not fun, and it’s definitely not what you want your visitors to see. A corrupted index.php file is a common reason for…

How to Check if Google is Indexing My Site? – 4 Easy Methods
You just launched a shiny new site. You’ve put in hours crafting content and setting it all up. Now, you eagerly wait for it to appear in Google search results….
How can we help you?
If you’re worried that your website has been hacked, MalCare can help you quickly fix the issue and secure your site to prevent future hacks.

My site is hacked – Help me clean it
Clean your site with MalCare’s AntiVirus solution within minutes. It will remove all malware from your complete site. Guaranteed.

Secure my WordPress Site from hackers
MalCare’s 7-Layer Security Offers Complete Protection for Your Website. 300,000+ Websites Trust MalCare for Total Defence from Attacks.